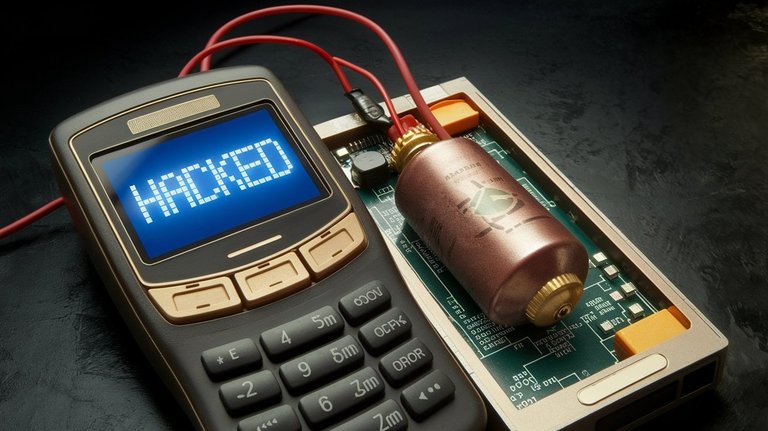
Tampering with pagers, turning them into a targeted improvised explosive device, has implications to cybersecurity and supply chain security. It is a bold and innovative attack, requiring serious planning and hardware tech skills.
My guess is that the firmware was modified to electrify the detonator when an intentional specific error message was sent. This allowed for selective targeting, could amplify the desired impacts based upon timing, and other conditions.
The small amount of explosive would limit the collateral damage, while still relatively confident that the device would be close to the body or near the face. If the attackers first sent a dummy text to get the targets to lift the device to their face to read it, then quickly followed with the malformed text, it would be devastating. But even if they didn't, pagers are usually kept near the waist, on a belt or in a pocket, which is near major blood vessels.
This employed true spycraft skills that leveraged the dependency of digital communication systems of their targets. I believe that such a long-term operation also necessitated an insider for distribution of these devices to the target community. I would also expect that the communications of these pagers were being monitored as well.
News stories about this event can be read here: https://news.yahoo.com/hundreds-pagers-exploded-lebanon-syria-191132472.html
Kind of makes me look at my phone with a little suspicion!
This is scary stuff. I have seen various stories saying it could have just overloaded the battery, but others say there must have been some explosive in there. Either way, it was very carefully planned and they must have expected to hurt some innocent people. I am sure more will come out about it.
Tremendous planning, coordination, and secrecy is required for such an operation. I think it is most likely a small amount of explosive was used and the battery just added to the burn cycle.