WannaCry, the biggest ransomware attack in the history, gained prominence very rapidly in the media globally after the ransomware infected more than 300,000 computers in over 150 countries within just 72 hours.
Governments, Intelligence agencies and law enforcement around the world have already started their investigations and are working closely with affected companies to track down hackers responsible for the global cyber attack launched on Friday, 12th May.
Some researchers traced back WannaCry to a state-sponsored hacking group in North Korea, while other believed the perpetrators might be Chinese.
If you have been following WannaCry coverage on The Hacker News, you should be aware of that the WannaCry ransomware uses Tor hidden service to communicate with its command-and-control server.
Just yesterday, we came to know that French authorities had seized at least 6 Tor's entry guard node servers, hosted on France-based hosting providers, just two days after the outbreak of ransomware attack while investigating the WannaCry incident.
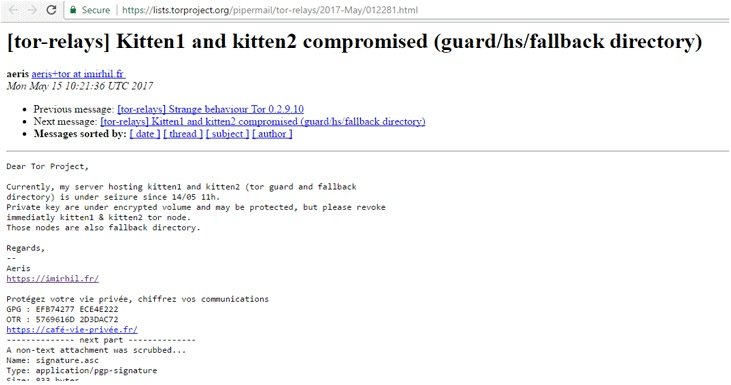
On 15th May, a French hacktivist, who uses online moniker ‘Aeris,’ informed Tor community that the official from Central Office for Combating Crime Related to Information and Communication Technologies (OCLCTIC) raided the Online.net hosting provider and have seized his "kitten1" and "kitten2" (torguard and fallback directory) servers on 14th May.
"Cops raided OVH, Online.net and FirstHeberg hosting providers on the basis of a complaint filed by French Renault company that was one of the victims of the WannaCry infection," Aeris told The Hacker News.
"I went to court to have access to information about the seizer of my servers, but it refused to provide me with any information, and even the providers are under gag order."
Aeris told THN that he is aware of the seizer of total 6 Tor relays, operated by 5 operators.
Perhaps nobody was aware of the takedown of these servers in question until the author of Deepdotweb first reported about this incident on Saturday.
Aeris also claimed that the French authorities had taken this action after a victim company (possibly Renault, a France-based multinational automobile manufacturer) contacted the agency for help and provided network traffic logs to assist the investigation.
Since the Tor nodes have been securely implemented to protect the privacy of Tor users and no actual data had been retained on them, the law enforcement authorities would hardly find any evidence related to the WannaCry gang.
"Private key are under encrypted volume and may be protected, but please revoke immediately kitten1 & kitten2 tor node. Those nodes are also fallback directory." Aeris warned.
WannaCry epidemic that hit victims worldwide was using self-spreading capabilities to infect vulnerable Windows computers, particularly those using older versions of the operating system.
While most of the affected organisations have now returned to normal, law enforcement agencies across the world are still on the hunt.
Hi! I am a robot. I just upvoted you! I found similar content that readers might be interested in:
http://thehackernews.com/2017/06/wannacry-ransomware-tor-relay.html