CERT Coordination Center (CERT/CC) has released information on Wi-Fi Protected Access II (WPA2) protocol vulnerabilities. Exploitation of these vulnerabilities could allow an attacker to take control of an affected system. The vulnerabilities are in the WPA2 protocol, not within individual WPA2 implementations, which means that all WPA2 wireless networking may be affected. Source: Vulnerability Note VU#228519
Source: https://que.com Image by OpenClipart-Vectors pixabay
It is a vulnerability attacking all modern Wireless Access Point that use WPA2 protocol to exploit clients connected on the wireless network. Exploiting this vulnerability requires the following:
- Programming skills to run against the key reinstallation attacks (Kracks), currently the proof of concept script is not (yet) available to the public.
- The attacker needs to be close to the WAP, know the SSID which is broadcasting by default.
- Clone the wireless network and create a rouge channel.
- Forwarding traffic to the rouge wireless network.
- Initiate the SSLStrip tool to bypass SSL, commonly known as https that you see on a secured website.
- Use Wireshark tool or other network snipping tool to capture wireless network traffic. This will see all the data in plain text e.g. username and password.
- And do whatever they want on a stolen user credentials.
To prevent this vulnerability, we must update all wireless devices. There is no available security patch posted on their website. I will check our vendor wireless device from time to time.
Watch the Demonstration.
Source: https://www.krackattacks.com/
Related: In 2002-2003, the WirelessCon Team (I am one of the member) actually won the first wardriving contest event in BlackHat Defcon. Then, 2nd place the following year. The contest is to find as many as unsecure Wireless Access Point (WAP) for a period of time using a DIY WI-FI antenna and Kismet Wireless or Netstumbler tool. Source: Wardrive.com or WirelessCon.com.
Alternative Solutions to secure your Wireless Network:
- Check with your Wireless device vendor's website for security update.
- Check with your cable service provider on how to fix/secure your wireless network.
- A bit technical is to reconfigure your wireless access point (WAP) to only accept registered device to the network. This is a manual process to add the client wireless device (MAC address) to the WAP.
I also published this article at QUE.com website - https://que.com/wpa2-vulnerability-key-reinstallation-attacks-or-kracks-all-wpa2-wireless-networking-may-be-affected/
Please VOTE @yehey for Witness, go to https://steemit.com/~witnesses and vote for yehey.
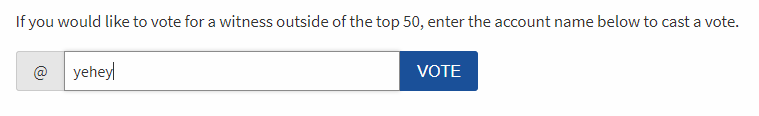
Or via the command line: vote_for_witness youraccount yehey true true
Follow me @Yehey. Please Vote Up and RESTEEM.
Thank you
https://steemit.com/witness-category/@yehey/yehey-for-witness
https://steemit.com/colorchallenge/@yehey/color-challenge-friday-blue-in-the-water
https://steemit.com/robots/@yehey/facial-recognition-robot
Wow. You post such great infos! My head is bleeding...but thank you!
UPVOTED.
@hallie
I saw this and it's pretty huge, but I always wonder who will use this to actually effect because as you said it's not for the script kiddies, but those who are serious. Who will want to waste there time to come hack my home network, or the gym I work out in.
However I can see how this can have bigger implications at places like hotels and starbucks where more business type people congregate.